CyberArk and BeyondTrust are some of the best providers of identity and access management (IAM) and privileged access management (PAM) solutions for enterprises. CyberArk works by combining the use of Adaptive MFA, SSO, Lifecycle Management, Directory Services, and User Behavior Analytics to protect the identities and critical assets of workforce users, privileged users, and third-party vendors when they access sensitive data. BeyondTrust is well-rooted in zero trust principles and works by offering an identity-first security approach that allows users to detect threats across their entire identity estate and respond by controlling privileges, credentials, access and secrets.
Both CyberArk and BeyondTrust are powerful, highly rated IAM and PAM systems that many users rely on, but which should you choose?
This article compares the features, capabilities, and pricing of the two solutions to help you make an informed decision about which one suits your needs.
1
NordLayer
Employees by company size
Micro (0-49), Small (50-249), Medium (250-999), Large (1000-4999), Business (5000+)
Small (50-249 employees), Medium (250-999 employees), Large (1000-4999 employees), Enterprise (5000+ employees)
Small, medium, large, company
2
twin door
Employees by company size
Micro (0-49), Small (50-249), Medium (250-999), Large (1000-4999), Business (5000+)
Medium (250-999 employees), Large (1,000-4,999 employees), Enterprise (5,000+ employees)
Medium, Large, Company
CyberArk vs. BeyondTrust: Comparison
CyberArk and BeyondTrust are similar in many ways. The following table summarizes the important features available on the two platforms.
| Characteristics | CyberArk | Beyond trust |
|---|---|---|
| Security focus | Accounts | Assets |
| Password Vault | Yeah | Yeah |
| Multi-factor authentication | Yeah | Yeah |
| Password management | Yeah | Yeah |
| Accounts administration | Yeah | Yeah |
| Privileged access management | Yeah | Yeah |
| Threat detection | Yeah | Yeah |
| Free Trial | Yeah | Yeah |
| Organization | Account | Host |
| Visit CyberArk | Visit Beyond Trust |
CyberArk and BeyondTrust Pricing
CyberArk and BeyondTrust pricing is based on the specific solution you choose.
Quotes are only available by contacting their sales team.
Feature Comparison: CyberArk vs BeyondTrust
CyberArk and BeyondTrust offer many features aimed at secure identity management.
Password management
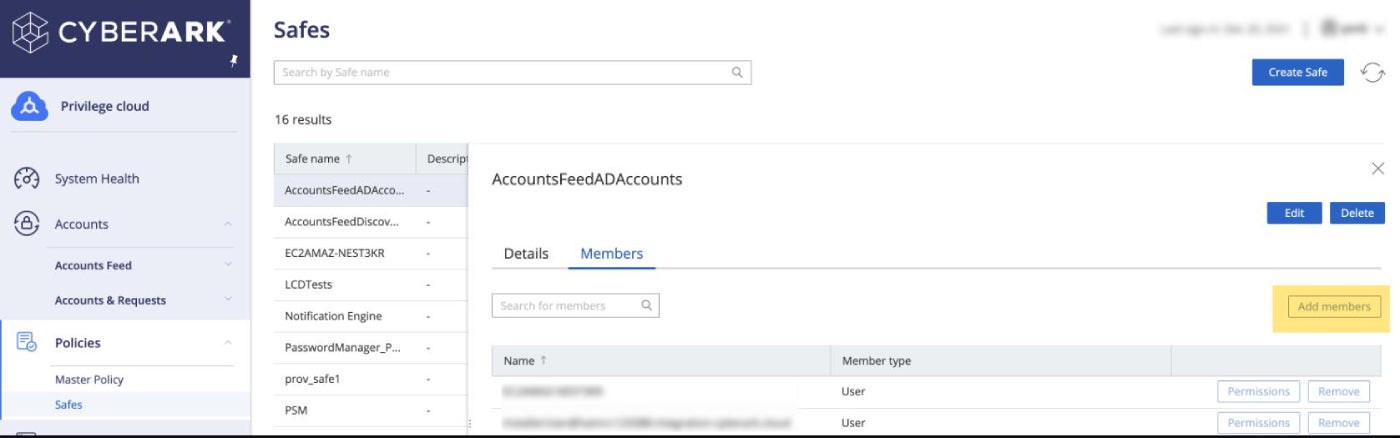
CyberArk offers workforce password management solutions that securely store, manage, and share business application credentials among employees. With this feature, users can automatically capture and store credentials in CyberArk's secure vault. This feature also allows users to share credentials and notes while controlling the permissions of their resource ownership rules.
BeyondTrust has a similar solution in Password Safe, a feature that ensures you have full control and responsibility over your organization's privileged accounts. The feature has a custom approval technique for user access requests and authentications.
Privileged access management
CyberArk's account-centric approach is based on managing privileged access, account user behavior, and account privileges. Through CyberArk's Privileged Session Manager, companies can protect, control and monitor privileged access to network devices.
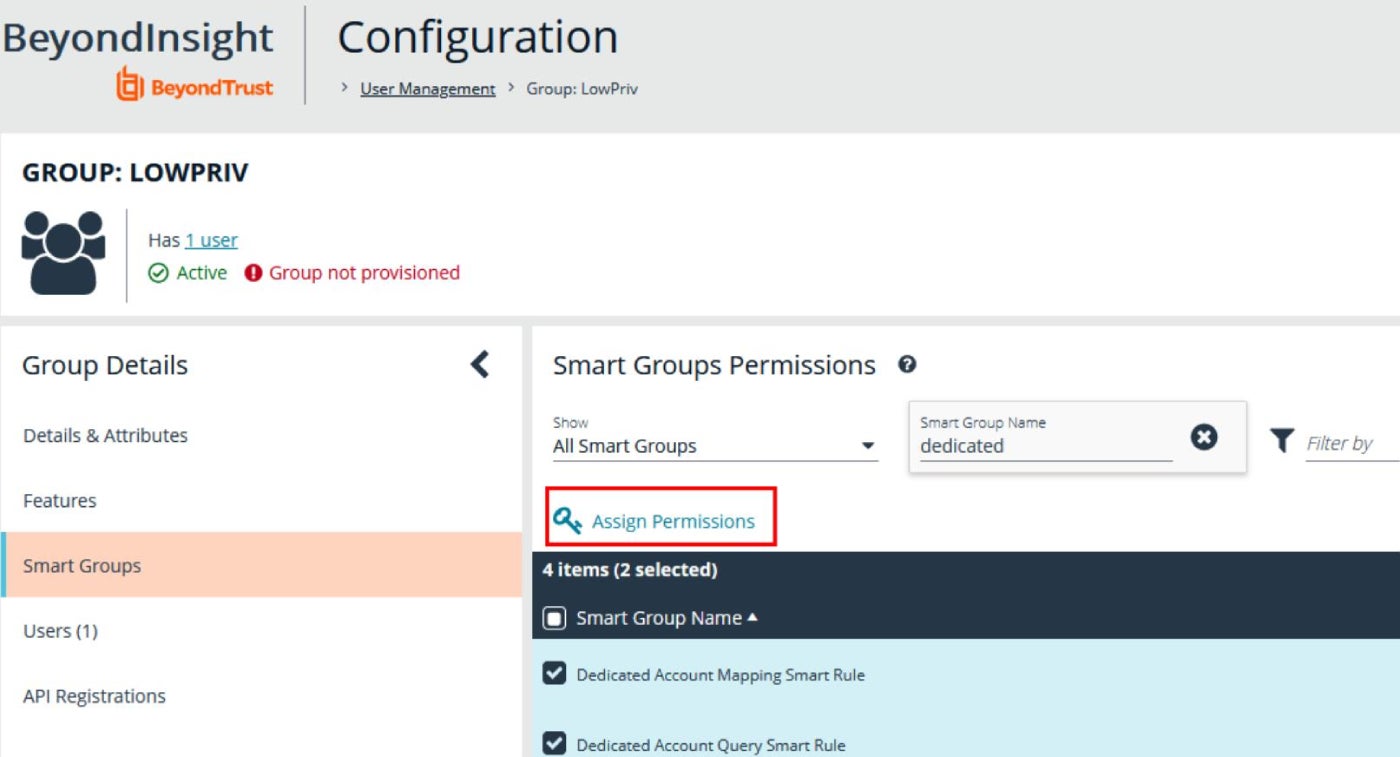
In contrast, BeyondTrust is asset-centric and the approach relies on environmental scanning to protect the organization's digital assets. The platform supports remote access and offers agentless asset discovery to help organizations audit their systems and understand where vulnerabilities may exist. It also has an Endpoint Privilege Management solution that elevates privileged access to known and trusted applications that require them, monitors application usage, and records and reports privileged activities.
Simplicity and ease of use
For beginners, CyberArk has a substantial learning curve. Many small and medium-sized organizations may be forced to hire a professional to implement the solution instead of implementing it internally. While documentation is available, it may be incomplete and inconsistent. A managed services provider may be needed for an organization to transition to CyberArk.
Comparatively, BeyondTrust solutions are quite simple to use and implement. BeyondTrust has a variety of features such as Smart Rules, Smart Groups, and Direct Connect, all aimed at facilitating the overall BeyondTrust user experience, thereby improving overall productivity.
Audience
Although CyberArk can theoretically manage up to 100,000 endpoints, the maximum real-world deployment is 57,000. However, CyberArk is more likely to be used by enterprise-level organizations, while BeyondTrust is more popular among small and medium-sized businesses.
CyberArk's features, functionality, and complexity are best suited for an enterprise-level organization. Meanwhile, BeyondTrust's simplicity, ease of use, and easy implementation make it a better choice for smaller businesses and mid-sized organizations.
Interfaces
The features and functions provided through the CyberArk web interface are not always the same functions provided elsewhere, which can cause confusion, especially in terms of API configuration.
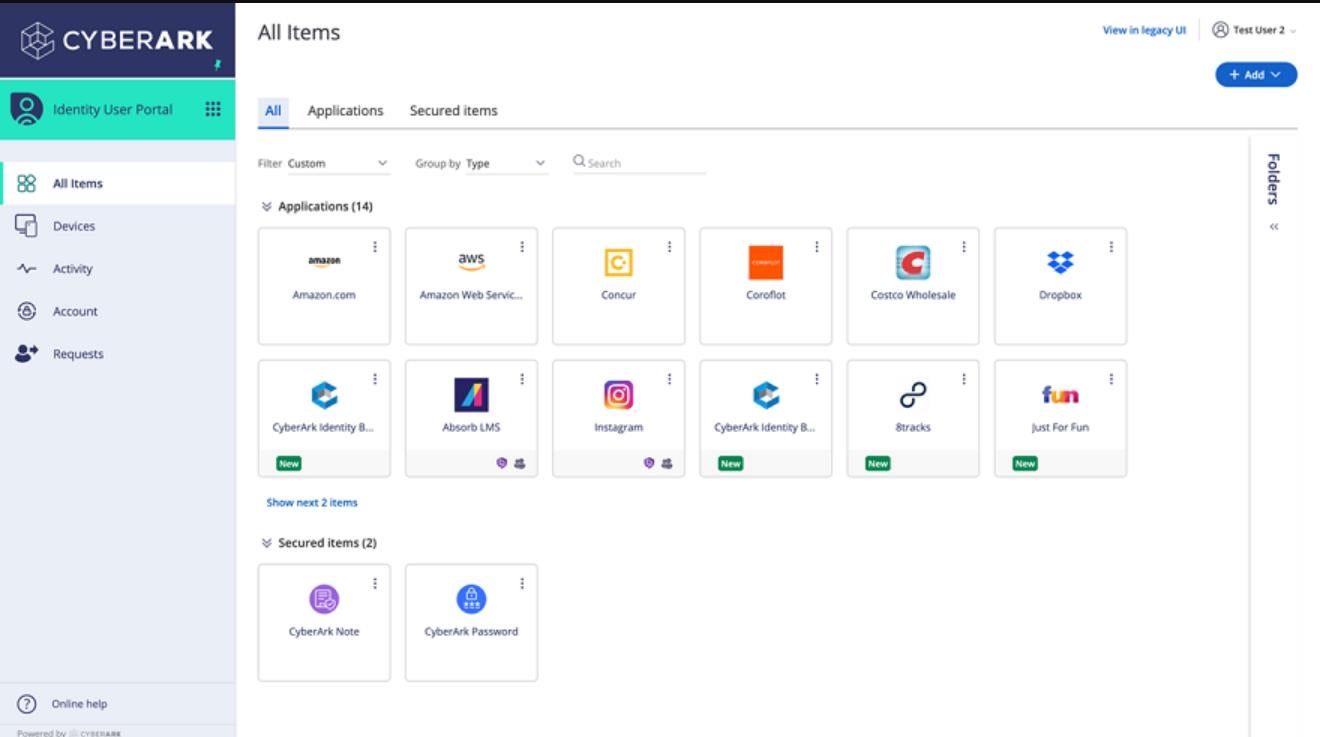
BeyondTrust provides a clean and attractive interface, although some users find it lacks more advanced features such as group approval. While BeyondTrust's interface may not have as robust a feature set as CyberArk, it is easier to use.
Pros and cons of CyberArk
While there are many advantages to using CyberArk for identity and access management, there are still some drawbacks to consider.
Advantages of CyberArk
- It integrates very well with on-premises and cloud-based data centers.
- CyberArk vault is good for compliance needs.
- Enables privilege controls across the entire IT environment.
- Provides identity threat detection.
- CyberArk has a free demo and trial option.
CyberArk Cons
- It can be complex to configure.
- The pricing model is complex. Requires a personalized plan from the sales team.
Pros and cons of BeyondTrust
There are some advantages to using BeyondTrust. However, the platform also has its disadvantages.
BeyondTrust Advantages
- It is easy to maintain and implement.
- It has an identity-first approach to security.
- Allows users to secure remote access to any infrastructure.
- It can detect and respond to security threats.
- Integrates well with technology providers like AWS, SailPoint, Ping Identity, etc.
Cons of BeyondTrust
- The price is not well defined.
- BeyondTrust remote support costs can be expensive for small businesses.
Methodology
We evaluated both CyberArk and BeyondTrust in terms of their IAM capabilities. During testing with the free trial available on both platforms, we took note of how key capabilities such as threat detection, secrets management, and privileged access management work. We find that CyberArk's features, functionality, and complexity are best suited for an enterprise-level organization. Meanwhile, BeyondTrust's simplicity, ease of use, and easy implementation make it a better choice for smaller businesses and mid-sized organizations.
We support our research by analyzing user reviews and Gartner testimonials to evaluate the performance of each solution in terms of user interface and overall user experience.
Should your organization use CyberArk or BeyondTrust?
CyberArk and BeyondTrust are fairly evenly matched IAM solutions that have a lot going for them. Today, BeyondTrust is one of the leading competitors in the field, but CyberArk is close behind.
Choose CyberArk if:
- You need a comprehensive IAM solution that can support on-premises, hybrid, and cloud environments.
- You need an IAM solution with built-in privileged access management capabilities.
- You're interested in an IAM solution that prioritizes account management and security.
- You are not afraid of a complex IAM solution.
Choose BeyondTrust if:
- You need an IAM solution focused on secure remote access and compliance with regulatory standards.
- You need an IAM solution with robust vulnerability assessment and patch management capabilities.
- You are interested in an IAM solution that prioritizes asset management and security.
- You need a solution that is quick and easy to implement.
Ultimately, CyberArk and BeyondTrust are powerful IAM solutions that can help organizations manage their critical assets and protect against data breaches. When choosing between them, first consider your organization's needs, requirements, and resources.
This article has been updated from a previous version published on May 2, 2022; It was originally written by Jenna Inouye.